0 Σχόλια
0 Μοιράστηκε
19201 Views

Αναζήτηση
Ανακάλυψε νέους ανθρώπους, δημιούργησε νέες συνδέσεις και κάνε καινούργιους φίλους
- Παρακαλούμε συνδέσου στην Κοινότητά μας για να δηλώσεις τι σου αρέσει, να σχολιάσεις και να μοιραστείς με τους φίλους σου!
- Building Resilient Cyber Defenses: Insurance Strategies for Small BusinessesCybersecurity breaches are increasingly common among small and medium businesses (SMBs), making them ideal targets for cybercriminals. Due to limited budgets, lack of expertise, and the misconception of being “too small to be targeted,” many SMBs operate with minimal cybersecurity defenses. Unfortunately, this vulnerability is exactly what cyber attackers rely on, exploiting weak...0 Σχόλια 0 Μοιράστηκε 14160 Views
- How to Implement Cyber Threat Hunting: A Complete 2024 GuideAs cyberattacks become increasingly complex and frequent, traditional cybersecurity measures are struggling to keep pace. Firewalls, antivirus software, and even intrusion detection systems are no longer sufficient to protect modern organizations. In 2024, businesses are likely to face sophisticated threats such as advanced persistent threats (APTs), ransomware, and insider attacks—many...0 Σχόλια 0 Μοιράστηκε 10127 Views
- Ultimate 2024 Guide to Implementing Cyber Threat HuntingAs cyberattacks advance in their sophistication and frequency, traditional cybersecurity defenders-the firewalls, antivirus software, even intrusion detection systems-are no longer sufficient in protecting companies. Organizations are bound to face advanced persistent threats (APTs), ransomware, as well as insider attacks in 2024 that often go undetected by automated detection tools. This makes...0 Σχόλια 0 Μοιράστηκε 10489 Views
Προωθημένο
Προωθημένο
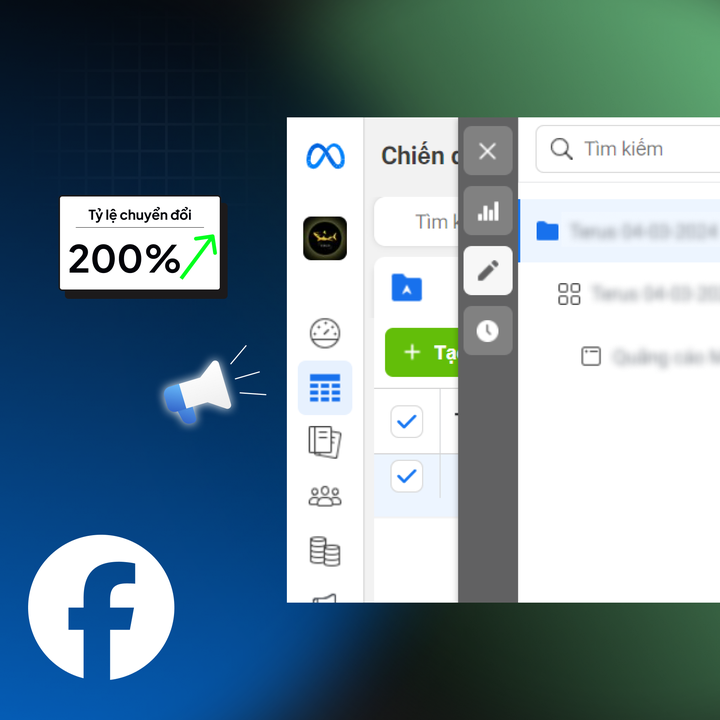
Liên Hệ Quảng Cáo